IBM Vault 2.0: A User-Friendly Overhaul with Enhanced Reporting and Onboarding Tools
IBM Vault 2.0 marks a significant shift in making secrets management more accessible. With a focus on reducing complexity, the update introduces a visual policy generator, onboarding wizard, revamped navigation, and improved reporting. These enhancements help users adopt best practices faster without needing deep Vault expertise. Below, we answer common questions about the new features and how they improve visibility and onboarding.
What are the main goals behind the UI enhancements in IBM Vault 2.0?
The UI overhaul centers on two key pillars: discoverability and adoption. First, IBM wanted to help customers easily understand and discover new features without requiring them to be Vault documentation experts. This meant mapping features directly to customer problems. Second, the goal was to enable customers to quickly adopt features using best practices, strengthening their ability to deliver their own roadmaps. By reducing the learning curve, IBM Vault 2.0 allows teams to onboard without needing a "PhD in Vault." The enhancements ensure that common tasks—like writing policies or configuring secrets—are guided and intuitive, lowering the barrier to entry for new users.
How does the visual policy generator help new users?
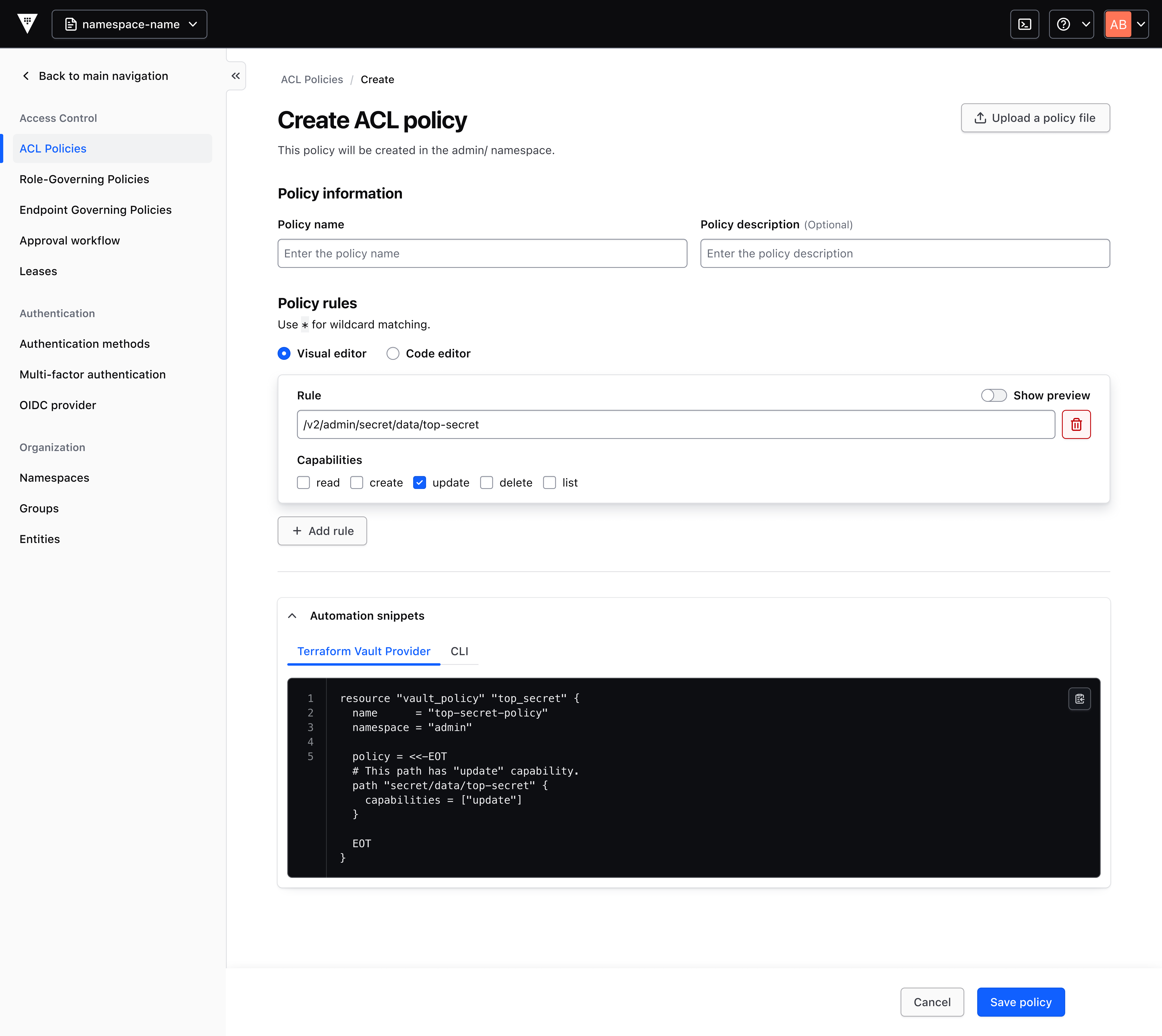
New Vault users start with no permissions, and assigning access requires writing custom policy code—a steep learning curve. The visual policy generator in Vault 2.0 solves this with a pre-filled, contextual UI form that generates policy snippets. Users select options in the interface, and the tool produces best-practice policies ready to copy. These snippets can be used with the Terraform Vault Provider (recommended) or saved directly to the Vault cluster. This feature reduces the operational burden on administrators and removes a barrier to feature adoption, allowing users to grant permissions quickly and correctly without memorizing policy syntax.
What is the onboarding wizard and how does it work?
The onboarding wizard is a guided tool that starts with simple questions about how a user plans to use a Vault feature. Based on the answers, it generates an editable code snippet that supports that specific use case. For example, if a user wants to store database credentials, the wizard asks about the database type and access patterns, then produces a tailored configuration. This hands-on approach helps users learn by doing, and the code can be fine-tuned later. The wizard is part of IBM's effort to match features intuitively to customer problems, making it easier for teams to adopt Vault without extensive training or reading through manuals.
What improvements were made to navigation and introductory pages?
Vault 2.0 introduces a revamped navigation bar that groups features by customer problems rather than by technical categories. This centers the customer experience—users can find relevant tools based on what they need to accomplish, such as "manage secrets" or "set up access control." Additionally, introductory pages for both new and existing features explain the value add and recommend a quick-start action. These pages provide context and a clear starting point, helping users understand how a feature solves their problem before diving into configuration. Together, these UI changes reduce confusion and accelerate onboarding.
How does Vault 2.0.1 improve reporting and visibility?
Version 2.0.1 brings enhanced reporting into consumption, giving organizations deeper insight into how Vault is used across secrets management, key lifecycle management, identity brokering, and data protection. These improvements provide greater transparency into usage patterns, enabling teams to monitor operational visibility and support forecasting, planning, and governance initiatives. For example, administrators can see which secrets are accessed most frequently, identify unused keys, and track policy changes. This data helps optimize configurations, plan capacity, and ensure compliance, turning Vault into a more accountable and manageable tool.
Why did IBM focus on onboarding and adoption in this release?
IBM recognized that many Vault users struggled with the product's complexity, especially when starting out. Although numerous educational resources exist—from developer docs to community content—they are often disconnected from the product itself. To become a Vault expert, users had to piece together disparate knowledge. With Vault 2.0, IBM aimed to contextualize knowledge within the product, so users could learn as they work. By reducing reliance on external resources and making the UI guide users through tasks, IBM lowers the time-to-value and helps customers adopt secrets management best practices more naturally. This focus on streamlined onboarding ensures that both new and experienced users can maximize Vault's potential without unnecessary friction.
What resources exist outside Vault to help users?
Beyond the product itself, users have access to a wealth of external resources. Developer docs provide detailed reference material, while videos created by HashiCorp (an IBM company) offer tutorials and walkthroughs. The user and community-generated content includes blog posts, forums, and open-source examples. These resources can deepen expertise, but they require users to actively seek them out. Vault 2.0 aims to minimize this reliance by bringing guidance directly into the interface. However, for advanced use cases or in-depth learning, these external materials remain valuable complements to the improved in-product experience.
How does the policy generator streamline assigning permissions?
In earlier versions, assigning permissions meant writing policy code from scratch—a tedious and error-prone process for administrators. The visual policy generator in Vault 2.0 simplifies this by offering a form-based interface that generates pre-filled policies following best practices. Users fill in details like the entity, path, and allowed actions, and the tool outputs the equivalent HCL or JSON policy. This code can be directly copied into the Terraform Vault Provider for Infrastructure as Code or saved to the Vault cluster. By reducing manual coding, the feature not only saves time but also minimizes mistakes, making secret management more secure and efficient for teams of all sizes.