Secure Identity for Agentic AI with SPIFFE
The rise of autonomous AI systems—from LLM-powered bots to robotic swarms—introduces a pressing challenge: how do these non-human entities prove who they are and establish trust? Traditional identity methods, built for human users and static credentials, fall short. Enter SPIFFE (Secure Production Identity Framework For Everyone), an open standard originally designed for cloud-native microservices. SPIFFE provides a scalable, cryptographically verifiable identity layer that fits perfectly with the dynamic, ephemeral nature of agentic AI. Below, we explore how SPIFFE works and why it’s becoming essential for securing AI agents. For a deeper dive into zero trust, see How does SPIFFE support zero trust architecture?
What is SPIFFE and how does it provide identity for workloads?
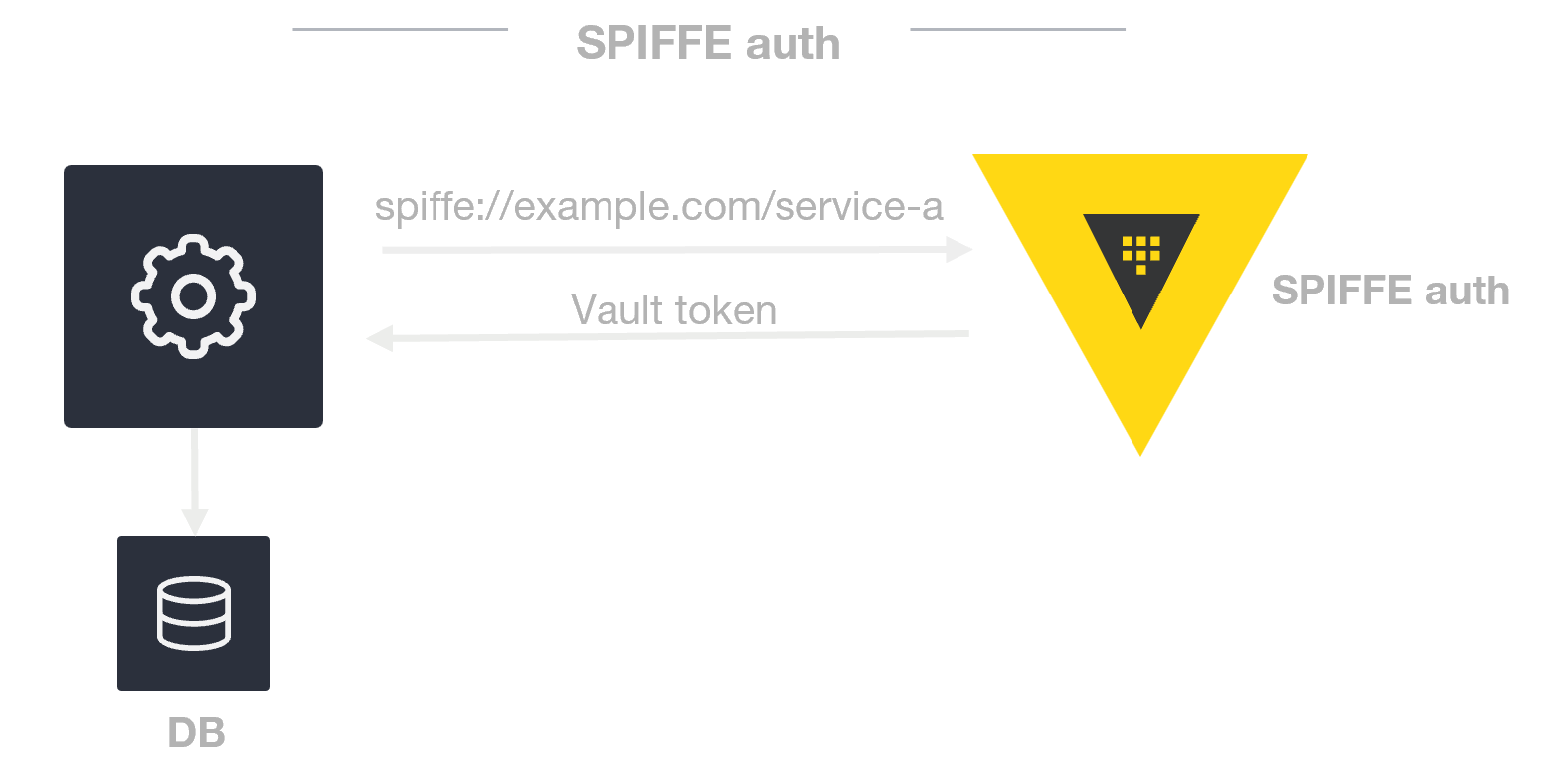
SPIFFE stands for Secure Production Identity Framework For Everyone. It is an open standard that defines a secure identity model for software workloads—services, processes, containers, and now AI agents. At its core, SPIFFE assigns each workload a unique identifier called a SPIFFE ID (e.g., spiffe://example.org/agent/traffic-controller). This ID is cryptographically bound to an X.509 certificate via the SPIFFE Workload API, allowing workloads to prove their identity without long-lived secrets like passwords or API keys. The framework also handles automatic certificate issuance, rotation, and revocation, making it ideal for dynamic environments. By decoupling identity from static credentials, SPIFFE enables secure, automated authentication across cloud-native and multi-agent ecosystems. It was originally developed for microservices but its principles apply directly to non-human entities that need verifiable, ephemeral identities.
Why is identity management critical for agentic AI systems?
Agentic AI systems—autonomous agents, LLM-powered bots, or robotic controllers—operate independently, make decisions, and interact with other services or agents. They need to prove their identity to establish trust, especially in multi-agent or cross-organizational environments. Without a robust identity framework, impersonation, data breaches, and unauthorized actions become serious risks. For example, a malicious agent could masquerade as a legitimate traffic controller in a smart city system, causing chaos. Traditional identity methods (e.g., static API keys) are fragile—they can be leaked, stolen, or hard to rotate. SPIFFE addresses these challenges by offering verifiable, workload-bound identities that are automatically rotated and revoked. It supports zero trust principles by ensuring every interaction is authenticated and encrypted. In short, identity management is the bedrock of secure, reliable AI operations in production.
How does SPIFFE enable zero trust architecture for AI agents?
Zero trust architecture assumes no entity is trusted by default, even inside a network perimeter. SPIFFE directly enables this by allowing AI agents to use mutual TLS (mTLS) for every communication. Each agent presents a SPIFFE-issued certificate containing its SPIFFE ID, and the receiving agent validates that certificate against a trusted root. This ensures that every interaction is both authenticated and encrypted, eliminating the possibility of impersonation or man-in-the-middle attacks. Moreover, because SPIFFE certificates are short-lived and automatically rotated, the window of exposure for compromised credentials is minimal. In a zero trust model, access decisions are based on identity and context, not network location. SPIFFE provides the foundational identity layer that makes fine-grained access control possible for agentic systems. For example, an emergency response agent could be granted temporary access to traffic controls only after presenting a valid, high-assurance SPIFFE ID.
How does SPIFFE handle identity federation across different domains?
Agentic AI systems often operate across multiple clouds, organizations, or trust boundaries. SPIFFE supports federation through a model where each domain (e.g., spiffe://org1 and spiffe://org2) independently manages its own identities. A bundle of trusted root certificates is exchanged between domains, allowing an agent in one domain to validate the certificate of an agent from another domain. This is similar to how public key infrastructure (PKI) works across different certificate authorities. SPIFFE's federation is designed to be lightweight and interoperable, enabling secure collaboration without requiring a shared identity provider. For instance, a weather monitoring agent from a government agency could securely share data with a city management agent run by a private contractor. The SPIFFE IDs carry provenance information, so each agent can verify the other's origin and trust level. This cross-domain trust is essential for complex, multi-stakeholder AI ecosystems.
How does SPIFFE accommodate the dynamic, ephemeral nature of AI agents?
AI agents are frequently created, scaled, and destroyed—sometimes within seconds. SPIFFE is built for this kind of dynamism. Instead of long-lived static credentials, SPIFFE issues short-lived X.509 certificates via a Workload API that agents can request on startup. The certificates are automatically rotated (often every few hours) without manual intervention. When an agent is decommissioned, its certificate is revoked, ensuring it cannot be reused. This reduces the attack surface significantly—even if a certificate is compromised, it is only valid for a limited window. Furthermore, the SPIFFE Workload API can be integrated with orchestration platforms (like Kubernetes), enabling seamless identity injection into new pods or containers. For agentic AI, this means that each instance of an agent receives a unique, verifiable identity from the moment it spins up, enabling secure authentication throughout its lifecycle.
Can you describe a real-world use case of SPIFFE with multi-agent AI systems?
Imagine a smart city where a swarm of AI agents coordinates traffic lights, energy grids, and emergency response. Each agent—say a traffic optimizer, a power grid balancer, and an ambulance pathfinder—must authenticate to each other before sharing data or issuing commands. Using SPIFFE, each agent is issued a SPIFFE ID like spiffe://smartcity/traffic/controller-a and a corresponding certificate. When the ambulance agent requests priority at an intersection, the traffic control agent validates its certificate via mTLS, ensuring the request is from a legitimate emergency system. The identity also carries attributes like ‘role:emergency-responder’ which can be used for authorization. Because all identities are short-lived and automatically rotated, the system remains robust even as agents are added or replaced. SPIFFE’s federation allows the city’s domain to trust an autonomous vehicle agent from a different manufacturer. This creates a secure, scalable foundation for multi-agent autonomy.